A few rather interesting developments in the Maricopa County, Arizona, ballot audit might begin to paint a picture of what possibly took place.
Let’s start with a letter sent by Senate President Karen Fann to the Maricopa County Board of Supervisors. Make sure you read the full letter:
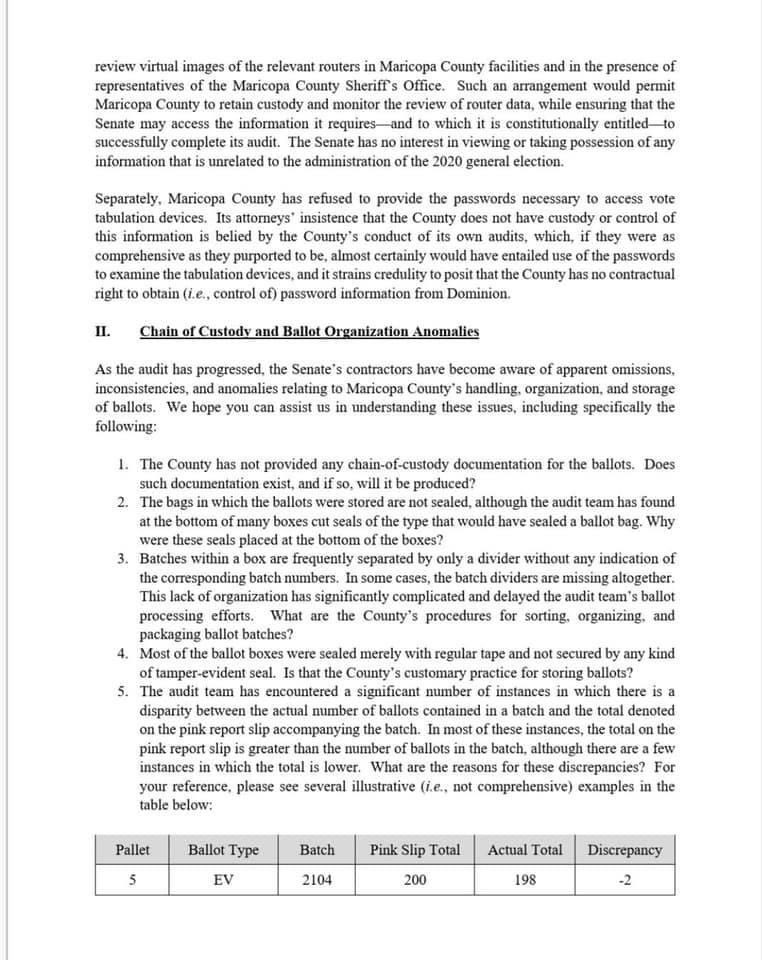
Here is where it gets interesting.
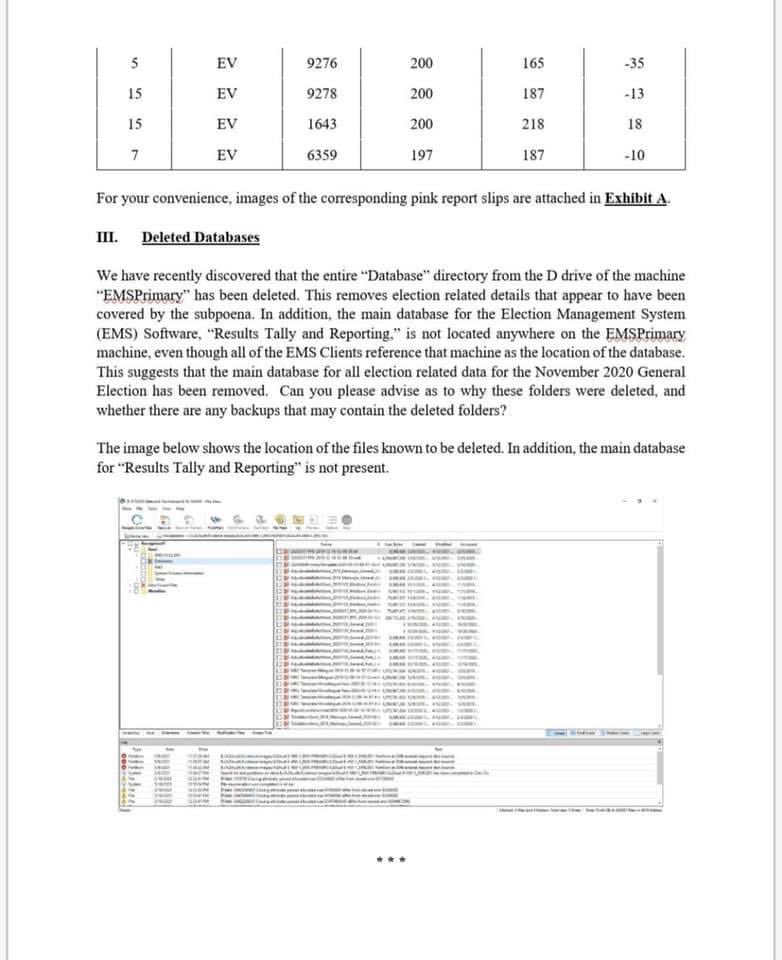
Let’s focus on the “database directory” that was found to have been deleted by the auditors. Pay attention to the dates ‘CREATED’ and the size of the ballot file size ‘bytes’:
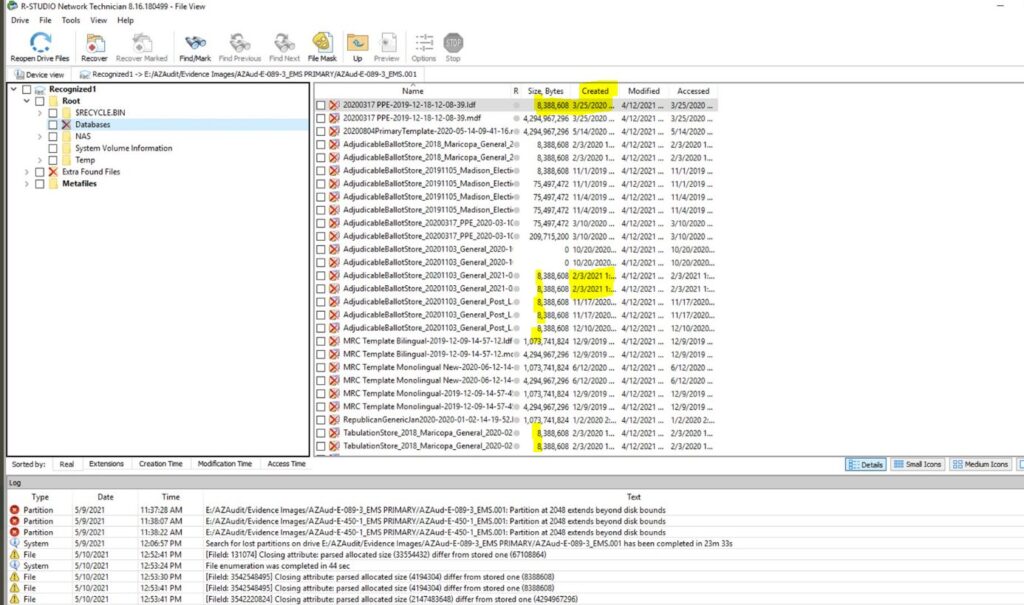
What are the odds the 2020 Democrat Presidential Primary Election file created 3/25/2020 would be the exact same size as the audited 2/3/2021 General election file?
Pres Primary file created 3/25/2020 8,388,608 bytes
General Election file created 2/3/2021 8,388,608 bytes
Notice the date this General Election file was created corresponds with the Maricopa Board of Supervisors being under pressure and holding a BOS vote on whether to audit the Maricopa County ballot results in an attempt to stop further public inquiry into potential misconduct. See this article link:
[Thursday January 27th, 2021] – “The Maricopa County Board of Supervisors will vote Wednesday on whether to conduct another audit on the county voting system in an attempt to placate any concerns of voter fraud or election misconduct during the 2020 general election.
The public can watch at 9:30 a.m. as the board considers an item at its public meeting that proposes “hiring two independent, qualified firms to independently audit tabulation hardware and software in a way that protects private voter information and our investment in the machines,” according to a statement from Chairman Jack Sellers.”
The article was written Wed Jan 26th, revised Thur Jan 27th. The “will vote Wednesday” is February 3rd, the same day the file was accessed.
On that February 3rd date the Arizona State Senate voted to hold the Maricopa County Board of Supervisors in contempt. See this article link:
[February 3, 2021] – All 16 Republicans in the Arizona Senate co-sponsored a resolution calling for the Maricopa County Board of Supervisors to be held in contempt and arrested for refusing to comply with wide-ranging subpoenas for election equipment and materials.
Senate Resolution 1005 directs Senate President Karen Fann to “take all legal action pursuant to section 41-1153” of state law, which says that any “witness neglecting or refusing to attend in obedience to a subpoena may be arrested by the sergeant-at-arms and brought before the senate or house.”
What this all means is yet to be determined; however, there is a general outline starting to emerge. Consider this scenario….
We know the 2020 Democrat President Primary was eventually coordinated by party officials, the DNC and the Obama network to put Joe Biden into place right before the 2020 South Carolina primary:
“Right before the SC Primary the DNC Club knew they had a problem with the Bernie Sanders momentum. An urgent assembly of all party control officers was called. The DNC Club designed a plan around using James Clyburn as the official spark for Joe Biden to take back control of the primary outcome.
 Former President Obama was initiated by the Club to contact all candidates and inform them when and how they would quit the race and fall-in-line behind Joe Biden. Clyburn was then triggered to initiate his endorsement and begin the rapid-fire process.
Former President Obama was initiated by the Club to contact all candidates and inform them when and how they would quit the race and fall-in-line behind Joe Biden. Clyburn was then triggered to initiate his endorsement and begin the rapid-fire process.
Within 48 hours all members of the club and candidates had their instructions and proceeded to follow-through on the plan. They had no choice. If they did not comply they would suffer the consequences of a fully aligned club hierarchy who would target them personally and financially. The plan worked flawlessly.
As part of the coordinated deal Representative James Clyburn was put in charge of the Biden campaign; Clyburn stunningly admitted this immediately after the strategy went public.”
Could it be that Maricopa County ballots (files) from the 2020 primary were used in the electronic tabulation machines as files to enhance the 2021 general election? If so, that would imply this strategy to manipulate the tabulation machines was in place for quite a long time prior to the November 2020 election.
We’ll have to wait and see how this plays out. What we know right now is the Arizona State Senate no longer wants background conversations with county officials; and instead wants the Maricopa county board of supervisors to appear for public hearings where the content and discussion is visible for everyone to see.
Interesting….
Jail the Election Board, all of them until they reveal who ordered this!
Have only state investigators involved.
Recover the deleted files, if possible. Without help from the DOJ or FBI.
So why delete a database?
Was this possibly a fabricated database with made up voter names?
And what percent of this deleted database voted for Biden? Would 90-100% be too obvious and thus the need to delete?
Just asking questions……..
Or, if they simply “inserted” the primary results into the general to boost Biden’s totals, was the database deleted to eliminate the discovery of names appearing multiple times?
Wonder how all of these Biden “voters” are going to feel when they are faced with the stark reality that President Trump was right about the Fake News, the Big Steal and the Big Lie? I, for one, don’t intend to play I told you so but I am hopeful that some are at least honest and forthright enough to admit that they have been lied to and deceived by the Democrat party and the Democrat leadership. I saw a meme yesterday where President Carter took the Worst President Ever trophy back from President Obama and presented it to Biden. Maybe the trophy should go back to President Carter. It should not be housed in a jail with Obama and Biden. This begs the question, does Biden even remember? We know that he knew since he told “We have put together, I think, the most extensive and inclusive voter fraud organization in the history of American politics.” This little slip may be the reason Biden keeps saying he’s going to be in trouble for answering questions!
Over 90% of the bite me voters will never believe anything else other than what they see and read from the fake news communist pravda media. I speak from personal experience. I have friends and relatives that believe all that crap, and I used to consider them pretty smart people. They have been completely brainwashed. Only a cataclysmic event might, MIGHT, get them to think otherwise. They are lost with no hope of purging themselves of the koolaid they have been force fed for year.s
Sadly true. They can’t come back without feeling a kind of pain from the realization that they have been completely fooled. The mind shys away from painful things. There’s clinical terms for it but you get the gist of it.
someone once said “it’s
easier to fool a person the second time, than to convince them they were fooled to begin with”
Biden will claim he’s suffering from dementia which is true and will not remember anything to cover his rear
Arizona State Senate based on this information should decertify the 2020 election, now.
So big deal, they just won’t show up next Tuesday and then what? Another letter? I want them thrown in jail now.
This is really getting old and showing the lack of any muscle to do anything about it.
Parked that bus in the wrong place. Now there are NO wheels left.
“Oh, what a tangled web we weave … when we endeavor … to deceive.”
Doesn’t Arizona have a state police agency with, like real, state troopers and guns? Isn’t organized election fraud by Maricopa County officials something that the state police typically investigate like investigating corrupt judges and zoning officials that take bribes? What am I missing here!
The will, to act! They should come down so hard on these people, that they can hear the thunder in Washington!
Snoopy; yes, the will.
What you’re missing is the State police take their marching orders from the very people who control their ranks. As a rookie patrolman in the 70s, first thing I learned was the little fish don’t eat the big fish.
The fraud was perpetrated by BOTH Democrats and Republicans. So the state Senate GOP will not carry through because they don’t want the Republicans exposed.
That is EXACTLY what most posters don’t realize. The RINOs knew what was going on and were happy w/removal of Trump and the retn of THEIR PARTY. THEIR PARTY gets them elected and they then make money. Trump was taking THEIR PARTY back and giving it to avg republicans. Trump had to go. The king had to be killed. RINOs were in on it.
There are Recon Rinos that infiltrate state politics and set up an underground network to take over the conservstive movement…
Romney =Utah
Chaney = Wyoming
Flake, McCain = Az
etc, etc.
Remove the current and previous Secretary of State for Arizona, and all Maricopa County election board members from office or involvement with elections for life. The Arizona senate should Certify President Trump as the winner of the 2020 election, now.
This is a straight up contempt of court issue. The Judge, should throw them all into jail until people start talking. WHO order this! He should be madder than hell!
For once, the red baron agrees with you. First to flip usually gets the best deal.
Of course, he should, but he is probably on the take just like everyone else.
Whoever “deleted” the data doesn’t understand journaling file systems or the Recovery Bin.
First step is to mirror the hard drive. Make a clone of it. after cloning, leave the original drive alone. Work only on the clone.
If the Recovery Bin wasn’t emptied, the files can be easily restored, just go to the bin, select the files, right click and restore them. If it was emptied, then the files were marked as empty space on the NTFS drive and space allocated as available in the MFT. More complicated, but not the end of the road.
There is also “Restore Previous Versions”:
If these don’t work, data recovery software is available ( some free, some paid ) that can help. A good one and steps to use is here, although there are others and I’m making no recommendation , this is just an example
https://www.easeus.com/data-recovery/ntfs-partition-file-recovery-freeware.html
If this doesn’t work, or there is other data corruption, there are “gravedigger” programs that can restore deleted data.
An example, again one of many, is https://www.diskinternals.com/ntfs-recovery/
For the curious: TWO copies of the MFT ( Master File Table) are stored on the drive. One at the beginning and one at the end of the drive (except (1993) Windows NT 3.51, where the 2nd copy is in the middle of the drive). The second MFT is called $MFTMirr. NTFS 5.1 has been in use since 2003. So, there’s a Mirror MFT that contains all of the metadata for the drive. There’s also the SAM file, which logs every user’s actions.
In other words, the identity of whoever deleted that database can be found, the files can be found and restored, and pretty much nobody can stop that. The tools to do so are many and powerful.
Lance states, “Whoever “deleted” the data doesn’t understand journaling file systems or the Recovery”
Wondering why you assume they only performed a simple “delete file” rather than a more comprehensive wipe, like with a rag…
My assumption is the auditors, if worth their pay, already checked MFT…
It is clear they don’t understand NTFS files and the Win OS because the rest of the drive contents remained intact. It was a simple file/folder delete. If it was a comprehensive wipe, there would be Zero files remaining. A totally empty, bare, formatted, drive. A comprehensive wipe would have been using DoD 5220.22-M protocol. Or degaussing the drive or putting a drill and hammer to work on it.
If the “data auditors” are anything like previous “ballot auditors”, they are likely the ones who did the delete.
No. Assume nothing. Seize the drive, clone it, and do a Professional Data Recovery.
In between a simple file/folder delete, and a comprehensive drive wipe, there are tools that wipe specific individually-selected files (like, with a rag), to those specs (or other specs). It is possible to step beyond the simple (and recoverable) delete while not going to a full drive wipe. Even the “unused empty” space can be wiped while leaving files intact (though that isn’t easy – but there are such tools).
Ok. Theoretically correct. But we are talking about humans in a hurry, dweeb election employees, trying to secretly delete a piece of information. If it is experienced I.T. people, so be it. Again I say “seize the drive, clone it, and do a complete forensic analysis for THAT file”. But. The SAM file contains the credentials and logs of whoever accessed that file. That’s why the SAM file is there and that’s what it does.
Unless the credentials are stolen, the bad actor is identified. Even so, interrogate the valid credential holder as to who/whom used those credentials. That universe is small. On to the multiple interrogations. Some low level worker is NOT going to jail to protect a Manager. Pigs squeal when squeezed.
Lance ‘.. I say “seize the drive, clone it, and do a complete forensic analysis ..”.
Yep. Standard forensic preparation.
A question is – is this audit one that contemplates possibly doing that sort of forensic work (or, more likely, having it done); or is it beyond their “scope”.
We shall see…
I’ve no idea what this audit contemplates. That isn’t my problem. Their scope isn’t my problem.
I’m saying that data creation, deletion, injection, all are logged by the OS and attached servers and can be audited forensically to identify attached devices, logged in people, all of their actions, etc.
There’s loads of “scope” flapping around.
I say seize the auditors, the Election Board officials, and anyone who has had access to the files since 3/20/20 and Manafort and/or Flynn them. That’s what the Democrats would have done.
Or, the data was stored in an external hard drive and never existed on the voting machine hard drive and that’s why it can’t be recovered… because it was never there. That also would explain why they won’t give up the routers if the data was flowing through the network to an external drive, or why Dominion won’t give up the admin passwords to the machines which would show functions (perhaps functions not even in the manual under technical auspices) that allowed an external hard drive to be attached to the voting machine and physically removed afterwards.
The technical people involved in the audit are not dunces Lance, they are qualified and if they cannot recover the data using recovery software methods it may be because the data was never on the hard drive to begin with. Some thoughts is all.
but you don’t necessarily disagree w Lance…. This isn’t necessarily a contradiction….
No. The voting machines originated the data. The original data originated in the voting machines. If external data was injected into them, their log files show it.
Every voting machine has an ID. If it had a modem attached, it had an IP address. The reason they won’t give up the servers is because the servers show all inbound and outbound IP addresses, timestamps, logs of everything.
Routers store nothing. They are data traffic switches. They keep no records.
Dominion won’t give up access passwords to the Dominion machines because those machines DO keep records and that data is stored on NTFS format drives where the SAM systems DO keep records of access identity, timestamps, etc.
The voting machine operating systems logs will show the UUID and DUID of attached devices. Because they are Win OS and NTFS systems logs. Attaching an external drive does not avoid the log files on the OS.
THAT is why Dominion won’t release the passwords.
I never said the technical people involved in the audit were dunces. I said the people involved in deleting the files were dunces. Worlds apart.
I applaud your imagination. The logs that matter are on the Dominion voting machines, not some imaginary external drive. The SAM logs and NTFS OS logs are on the voting machines. Those logs identify Who and What was connected to the system and When they were connected and disconnected and the file sizes transferred, when they were transferred and the UUID of the device.
We can imagine all kinds of scenarios. But let’s concentrate on the ones that matter.
Voting Machine OS Log Files. SAM log files. External drives don’t keep log files.
Every action on an NTFS file system leaves log files. Footprints. Fingerprints. Times, dates, filenames, filesizes, access ID, etc. Forensic nerds live for this. That’s what they do.
So, let me save us both some time on the next objection.
“A nefarious actor actually instructed the Dominion voting machines not to keep logs and/or they instructed the servers not to keep log files”.
Well. It’s possible. But what isn’t possible is to delete the SAM files that recorded those instructions on both the OS and the Server OS systems. One of them logged the instructions and the ID of the person who made those instructions. Bingo. We have a criminal ID.
If ANY of the log files were changed in ANY way, then ALL of the tabulated votes are Null and Void because the System is no longer a “certified system” and ALL of the tabulated votes are legally Void. As well, the entire precinct is legally questionable.
“Somebody’s got to go to jail”
I’m not objecting, simply expanding the discussion to encompass other possibilities. My opinion after reading the documentation being released from the various state audits, publicly available reports and publicly available databases compiled on the 2020 presidential election fraud, that sweeping criminal election fraud occurred in 2020 (and likely has been occurring in previous elections for many years). “Somebody’s got to go to jail.” 10/4!
Thank you for your patient explanation of the inner workings for those of us who are not very savvy.
iswhatitis “In between a simple file/folder delete, and a comprehensive drive wipe, there are tools that wipe specific individually-selected files (like, with a rag), to those specs (or other specs). It is possible to step beyond the simple (and recoverable) delete while not going to a full drive wipe. Even the “unused empty” space can be wiped while leaving files intact (though that isn’t easy – but there are such tools).”
Lance “Ok. Theoretically correct.”
I had meant to address this point, but forgot. So.. I’m back to address it.
What I had posted there is not merely “Theoretically correct”. It exists practically.
Here is a good example from Microsoft itself (but by no means the only existing tool):
SDelete
https://docs.microsoft.com/en-us/sysinternals/downloads/sdelete
Excerpt from the description:
“You can use SDelete both to securely delete existing files, as well as to securely erase any file data that exists in the unallocated portions of a disk (including files that you have already deleted or encrypted). SDelete implements the Department of Defense clearing and sanitizing standard DOD 5220.22-M …”
I’m not sure if you actually meant my assertion was only theoretical (or happened to choose inaccurate wording); but just in case you did think it was only theoretical, I decided to post an existing example showing that it isn’t.
What you cannot avoid is the SAM log that shows file access, timestamp, ID, filesize, etc.
I never said a file can’t be deleted. I said that deletion of the file leaves tracks. Also, the NTFS filesystem allows , via the OS, recovery of the deleted files, by means of various file commands.
If the SDelete command allows DOD 5220.22-M compliant deletion of files, it does NOT allow erasure of the OS log file and SAM file record of the Act of deleting the files. Nor the ID of the person who effectuated said command.
Firstly, prove that a DOD 5220.22-M file deletion occurred. Don’t speculate that it might have occurred. Show me the log files.
Secondly, show me the SAM files concurrent with said deletion and show me that the User ID was also erased.
Thirdly, show me the Server Log Files that connected all of these voting machines had their files also wiped at the same time and their security and ID files wiped simultaneously and then show me that the IP addresses were wiped.
I mean, really, we could all agree that Invisible Martians and Green Boogeymen conspired to do all these things and they all disappeared after their mission. In the real world, the OS on the voting machines and/or servers, contain all the records needed.
Criminals leave footprints. That’s what they do.
Lance “I never said a file can’t be deleted.”
True enough, you did not say that.
What you did say was that my assertion was theoretical.
I corrected that and showed it was not merely theoretical, but practical. Just setting the record straight.
What you did not do is show that the SDelete concept has relevance to the Dominion voting machine OS records or the Server OS records with respect to the SAM files and server related security records. I get that.
Just setting the record straight.
Synopsis:
You stated: Lance “It is clear they don’t understand NTFS files and the Win OS because the rest of the drive contents remained intact. It was a simple file/folder delete. If it was a comprehensive wipe, there would be Zero files remaining. A totally empty, bare, formatted, drive. A comprehensive wipe would have been using DoD 5220.22-M protocol. Or degaussing the drive or putting a drill and hammer to work on it.”
I pointed out that those weren’t the only two possibilities (simple file delete vs. comprehensive wipe):
iswhatitis “In between a simple file/folder delete, and a comprehensive drive wipe, there are tools that wipe specific individually-selected files (like, with a rag), to those specs (or other specs). It is possible to step beyond the simple (and recoverable) delete while not going to a full drive wipe. Even the “unused empty” space can be wiped while leaving files intact (though that isn’t easy – but there are such tools).”
You said that was a theoretical assertion. That is incorrect. So I corrected it.
I don’t need to gin up elaborate theories that satisfy you, in order to “show relevance” – I was pointing out facts – not opinions on what I think transpired (or not).
But if that’s where you want to go, just for the sake of arguing – I’ll point out that all the talk of SAMS and all that stuff you said, completely ignores that it can all be 100% bypassed. Your argument implies that it cannot. But whether you think personally it is likely or not is different from the fact that it can be (just like with the file erasure possibilities).
By conflating your opinion of what might have happened with the facts of the possibilities of what can happen, you may be underestimating your enemy. That’s your choice, and I respect it.
Still, all I did was point out that the two extremes you posited as the only two possibilities are not the only two possibilities. Instead of acknowledging that fact, you chose to denigrate it by calling it theoretical – which it isn’t. Being corrected on that point seems to have set you off.
fwiw I agree w you Lance, I have the feeling whoever deleted these files has no clue. Like the photoshopped pictures of Biden – they are trying to keep things to a small inner group and that group has no clue. Criminals running around in new fallen snow. Yes they can delete but they cannot delete to where nobody knows they did it, and they have to be incredibly good to really delete at all. A really good team can get it back. There’s a reason Hillary took a hammer to her secrets. I’m w you.
never assume that deleting anything is effective. Put a drill bit or a hammer through a disk drive.
crush/mutilate/destroy a SSD. Burn magnetic tape and punched paper records. Shred it all.
Only then can you believe your data is gone. But then again, if you were ever connected to the internet, it is possible that all of your data has been stolen. Maybe I’m paranoid. I have one computer to connect to the internet and it has nothing on it. My real computer is 2 meters away and never connected to the internet except for OS updates, and even then, very carefully.
It isn’t crazy thinking if there are actually people out there who will stop at nothing to retain their own power. I trust 3 people. 2 of them passed away years ago.
Lance, I do believe you are brilliant !! Thanks for giving is a small beam of hope.
I have been out of the game (Computer/Networking) for a number of years now but looking at the directory structure this appears to be a Network File Server using a Linux/Unix based file system.
We have a root directory and a NAS (Network Attached Storage) directory. I agree there appears to be a “System Volume Information” and “$Recycle.bin”, which would indicator a Windows based operating system but this would occur simply by mapping the Network File Server shared directory to a Windows based PC.
Typically files are recoverable if they are local drive, but files on a Network Share typically are not (unless the network server hosting the network share backed it up).
I know that you can mount a NAS share as a virtual “physical drive” (versus a Mapped Drive) but I’m not sure if that means the OS treats this the same as an actual physical disc connected to the PC.
Like I said, I’ve been out of the game for a number of years now, but the last time I had set up a NAS as drive storage for a digital surveillance camera network the NAS did not run on a NTFS file system.
On the other hand, if I remember right (and again, its been several years) I believe these NAS drives were mounted in Windows as if it was a physical drive and then formatted to NTFS but for some reason I believe that the NAS drives, although appearing like a local drive in Windows, still were treated more like a network share where the base system housing the drives (the NAS) were really in control over the file system of that network drive. I may be wrong… its been a long time.
I guess that would lead to the other question … where (physically) was this NAS and why would they be using NAS drives mapped to the system? In reality (without knowing more about how this system/network was set up) this NAS could have been anywhere on the network, or if connected to the Internet, anywhere in the world. This would be very insecure in my opinion as the NAS could be replicated and modified at any time than it’s connection restored to the PC it was mapped to with little to no indication of any change appearing at the local PC that was using it. (Or the NAS removed and a replacement restored at the same IP address, etc)
Again, I may be wrong here… I haven’t worked with this stuff in years….
I just wanted to throw that out there….
Hillary could introduce them to Bleach Bit.
Because the other data on the drive remained, a full secure drive wipe didn’t take place.
The SAM file logged the credentials of whoever deleted that database file. Somebody logged in. That login was logged. The SAM file remains because the entire drive wasn’t wiped.
Most users don’t have a clue about the $MFTmirr backup Master File Table or the SAM files. If the culprit was some kind of manager type and not an I.T. geek, it is very likely the deletion was a common file deletion.
My money is on ignorance, which is more common and most likely. Administrative type people ( not Data Administrators or SysOps) are usually not tech savvy. They know just enough to think they know something.
YES YES YES. No clue.
Lindell says he has “indisputable proof” that very technical foreign state hackers (mostly China) were involved. It’s also alleged in other sectors perhaps very technical domestic deep-state operators were involved.
Excellent response, but will they do this? Don’t even think about holding your breath!
I think I read a theory that the files were not deleted, but were always on an outside device/system/server.
‘Zona (You Changed Our Numbers)
Ari-Zona, what are you all up to?
You took something we fought to hold on to
You might think you’re facing loser RINOs
Who delight in your show as America falls
‘Zona, we got your number
We’re gonna make you shine
‘Zona, you changed our numbers
Eight-Three-Double-Eight-Six-O-Eight
Eight-Three-Double-Eight-Six-O-Eight
Eight-Three-Double-Eight-Six-O-Eight
Eight-Three-Double-Eight-Six-O-Eight
‘Zona, ‘Zona, we bet you’re uncomfy
You know we know you let down our whole country
We tried to play nice before then you wiped the servers
We see through your deformation of our bright futures
‘Zona, we got your number
We’re gonna make you shine
‘Zona, you changed our numbers
Eight-Three-Double-Eight-Six-O-Eight
Eight-Three-Double-Eight-Six-O-Eight
Eight-Three-Double-Eight-Six-O-Eight
Eight-Three-Double-Eight-Six-O-Eight
We got it, We got it
We got the number of you all
We got it, We got it
For a good time, for a good time call
‘Zona, we got your number
We’re gonna make you shine
‘Zona, you changed our numbers
Eight-Three-Double-Eight-Six-O-Eight
Eight-Three-Double-Eight-Six-O-Eight
Eight-Three-Double-Eight-Six-O-Eight
Eight-Three-Double-Eight-Six-O-Eight
‘Zona, ‘Zona who can you turn to?
Eight-Three-Double-Eight-Six-O-Eight
Who’ll drop the dime that destroys your sham virtue?
Eight-Three-Double-Eight-Six-O-Eight
Eight-Three-Double-Eight-Six-O-Eight
Eight-Three-Double-Eight-Six-O-Eight
Eight-Three-Double-Eight-Six-O-Eight
Eight-Three-Double-Eight-Six-O-Eight
(X4EVA)
At least they are Smart Criminals – they had the good sense to Destroy the Evidence that would have implicated them. Now all the Criminals have to say is “Huh? I don’t know what happened to the Database. It was there the last time I looked!”
No, they weren’t smart. The data can be recovered and restored. That is one of the strengths of the NTFS file system.
The SAM file will identify the credentials of whoever logged in and deleted the data. Tough for him/her.
If they were smart, they would have put a power drill through the drive or flattened it with a hammer.
You obviously know far more than myself and probably the same holds true for our community here. Worse case scenario, I believe you can recover the deleted information directly off the physical drive itself. Or have you already discussed that in one of your posts and my brain didn’t catch it?
On a not related issue, how can I be notified when someone has replied to a post of mine? I miss that feature, which I had before the migration.
Well, Bill, I don’t know how notifications of replies work after Sundance had to create a new platform. That’s kind of up to him, and I’m a nobody.
Yes, data can be recovered from the physical drive, or the server it passed information to/from.
Daddy said “If you don’t want to be called out, don’t do nothin you wouldn’t do in front of me or your mom”.
Well, maybe some of that relaxed after I got married.
Here’s your modern day reference point:
mueller special counsel team CELL PHONES
???
I doubt the size comparison is significant. (“What are the odds the 2020 Democrat Presidential Primary Election file created 3/25/2020 would be the exact same size as the audited 2/3/2021 General election file?”)
That is the default initial size for MSSQL LDF files, and it’s possible that’s all those systems need for any election.
There are several files with other identical sizes larger than 8MB.
Not to lessen your alarm about possible/probable election fraud, database files are “different animals” than other computer files. They are allocated according to best guess of the maximum amount of data they will eventually hold. The .mdf files hold data, the .ldf files are log files for database transactions. They could be full, or they could be empty. The only way to know, is to start the database engine, and query the database. The access times, and modified times, are significant, and alarming.
Watching the Steve Bannon’s Warroom at https://rumble.com/c/BannonsWarRoom and heard that Faux News wasn’t covering this HUGE issue. So, went to the Faux News website and looked around and even searched “Arizona” and what did I find? NOTHING. Bottom line: DUMP FAUX NOW and support media that at least covers MAGA!
Will the AZ militia be forced to physically defend the auditorium against the feds? Surely there is a plan if federal troops surround the building. Waco. Ruby Ridge. The Bundy ranch. It’s nauseating to contemplate.
I am NOT a database expert but I have worked extensively with SQL for years. Sundance, don’t read much into the multiple files with the same number of bytes. The files that all have 8,388,608 bytes look like transaction logs (.ldf extension).. SQL always creates a log file for every Database file (.mdl extension) created. The log file is instanciated with a default size of 8MB which is actually 8,388,608 in binary.
The file size gives a pretty good idea of what file size to look for in a deleted file during a forensic data recovery.
Agree not to get worked up over instances of .ldf and .mdl files.
But it helps to know the file block size when looking for deleted files. Saves time by not looking for irrelevant files.
Sue or fire thise SObs.
I worked for a retail grocery store as a scanning Cordinator for many years. When corporate would send down our price changes we never knew how many changes we’d have. Our price changes would come down in batches, sometimes there were a lot of price changes. When we applied the batches it’d take sometimes 3 to 4 hours to apply all the batches. I’m wondering if the Democrats and Dominion were building batches and waiting till November to apply the batches. That’s why they shut down voting in several states. I’m also wondering if they’ll try again to do the same in 2022. How long have they been cheating? I’m guessing many years.
Weren’t there some suspicious shredded papers found in a dumpster. Hmmm could these be the missing ballots.
Get ’em!
One thing is certain.
Never use voting machines. Paper ballots only. With all the holograms, security features, etc.
It can be done.
I agree with others comments that the dates are interesting, but what I find more interesting in looking at the dates, is comparing them to the file names.
Some of the file names appear to correspond closely to when the file was created. MRC Template Bilingual-2019-12-9… was created on 12/9/2019.
Other files seem to have similar file naming conventions where the dates are included in the filename.
Not all though. It leads to the obvious question of why the first file shown, 20200317-PPE-12-18-12-08-39 was created on 3/25/2020.
All of the highlighted files have the same anomaly. That suggests files were deleted, with old files copied in their place, but the names were not changed to match the creation date. That would make things too obvious I guess.
Could they really have been this sloppy?
Delete the traitors. Thousand slow cuts.
Am feeling my age and lack of knowledge re electronic stuff re this post. But I get the big picture. I used to do this background work on my fed audits- but the communications only went to the auditee and were not open and public as they are in AZ.
Hard for me to absorb how the AZ documented questions are open for all to see. When in my time, such things were private communications and we just dropped the “bomb” at the end of the audit with our report along with our findings and recommendations. Think Horowitz style. Seems so archaic in retrospect.
After a long, cold, lonely winter up north, reading about all of the work being done to find the truth in the AZ election feels like “Here Comes the Sun, little darling, here comes the Sun. It alright.” And I’ve got a feeling, deep inside, oh yeah, this is all going to work out for the good.
The AZ audit is a CLASSROOM of LEARNING. And I am enjoying it heartily.
Two or three thoughts on a problem with a router found in the secured counting area. I would have had the piece of equipment in plugged immediately. Next placed in an evidence bag. The people present not leave until evidence bag turned over to state or fed authorities. The republican witness should be handcuffed to the evidence. Mandatory that router be immediately cloned the copy given to the handcuffed witness whose then released. This copy given to senate and the original, forensic analyzed by Crowd strike to their hearts content. If any bad news the Senate can examine the copy and confirm or reject analysis. The problem I have is why do they need the routers to begin with. Doesn’t the Internet provider possess this data?
Well here is the good news… Being that they found the deletions, Rstudio has that fancy little “recover” button…
Which means the files are already in the Senates possession, which means they already know the answers.
Now make it public…
CDC says this, CDC says that. Exactly who is the CDC? Name the names of these self-serving bureaucrats that has much of America dancing like a bunch of idiots.
Looks like the “receipts “ are coming home to the DNC. Were these same Arizona tactics used in Wisconsin Pennsylvania Michigan Georgia Nevada and New Mexico?
Obama and his cabal were the Alinsky architects behind the Big Steal and they must be held accountable for the 2020 Insurrection throughout our country.
Unfortunately, most of those who actually DID vote for Biden aren’t intellectually savvy enough to understand the lengths to which Obama & Co went to steal the election. Ho Ho Ho Harris waits in the wings to take over but Sunday Susan Rice is actually running the puppet show in the White House following an Obama script. Baldacci couldn’t have scripted it much better!
Decertify the election results. Period.
Get the log files from the firewall.
Oh, and by the way, the County Commissioners told the Senate to stick it in their ear. Nice, huh?
2002 “Helping” America to Vote Act. Yeah they helped us alright.
Way past the time to hold ALL persons elected to public offices accountable for failure to follow laws.
They are supposedly employed by the tax payers to represent them, but lobbyists really hold the reins of those failing to comply with audits, & in general, ignore or circumvent the Constitution of the United States of America.